User Access Review
Access Control - UAR
The University's Cyber Security Policies and Standards require all access to University IT Services to be authorised, restricted based on need, and to be annually verified. Without periodic reviews of user access to applications, the University is at risk of unauthorised access, fraudulent activity, or confidentiality and privacy breaches.
The Cyber Security Guideline - User Access Review outlines the process, roles, and responsibilities for reviewing access and is a mandatory control required by the Cyber Security Standard - Identity and Access Control. A UAR revalidates user accounts and access rights associated with IT services and assets.
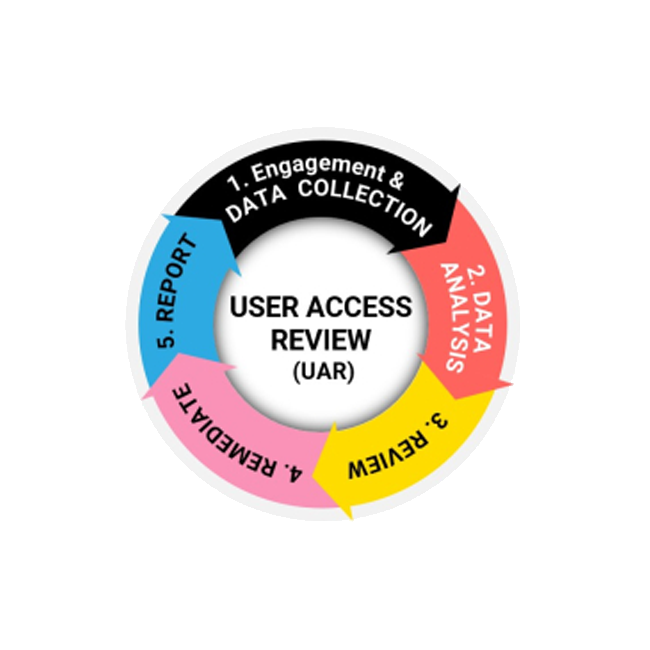
A UAR cycle involves engagement and data collection, analysis, review (validation), remediation, and reporting.
Current UAR underway
View the applications in scope for the UAR cycle 2025.
-
-
Applications targeted for a 2025 UAR cycle will be listed here.
- Applications in scope for the UAR cycle: 2025
Business Owner is a person with primary responsibility for the business or technology functions provided by one or more UNSW Information Resources, including any associated cyber security risk. Note: The Business Owner of a UNSW Information Resource may be in the UNSW IT unit or any other Organisational unit. Extract from the Cyber Security Standard - Identity and Access Management.
-
- To complete your review of accesses or view your past UAR cycles, open the MyUAR tool
by clicking on the image or enter: https://myuar.unsw.edu.au/ into your browser window. - Remember when making a review decision to submit your review before closing the browser window.
1. Guides and FAQs
2. IT UAR team
- For urgent questions, contact the UNSW IT UAR team via email cybersecurity-uar@unsw.edu.au.
- To complete your review of accesses or view your past UAR cycles, open the MyUAR tool
-
The following are involved in a UAR cycle:
Involved Responsible for Organisational Unit Heads Ensuring a formal process is in place to manage access rights associated with IT services and assets that are under the units' control. Business Owners Business Owners are responsible and accountable for:
- Ensuring their applications are compliant, with the Cyber Security Standard - Identity and Access Management, by completing the UAR. Business Owners may delegate this activity to the IT Service Owner, however, the Business Owner retains accountability.
- Scheduling and conducting access control verifications on the applications they are responsible for, as well as being accountable for data collection.
Extract from the Cyber Security Standard - Identity and Access Management.UNSW Managers
(anyone with staff reporting to them, e.g., Supervisors)UNSW Managers, anyone with staff reporting to them, e.g., Supervisors, are responsible for:
- Ensuring their staff access is validated by completing the UAR. Managers may delegate the review activity; however, it is not permitted to delegate a user's access review to the user themselves. In the case of missing manager or supervisor information, the access must be reviewed by the Business Owner.
- Providing, reviewing, and/or removing accounts and/or access for their direct reports.
- Keeping staff up to date on any changes to account access levels.
- Acting as an escalation point for action where they are the Manager Once Removed (MoR).
IT Service Owners
(IT System Owner)IT Service Owners are responsible for:
- Assisting Business Owners by providing user access lists for the applications they are responsible for.
'Information Service Owner means the person responsible for defining, operating, measuring, and improving a UNSW Information Service and associated cyber security controls. Also known as System Owner or IT Service Owner.'
Extract from the Cyber Security Standard - Identity and Access Management.UNSW IT Cyber Security UAR team Oversee the facilitation of a UAR cycle to ensure compliance with Cyber Security Policies and Standards.
Important:
- When conducting the review, reviewers (Business Owners, UNSW Managers/Supervisors, or their delegates) are advised to consider that staff may have more than one role across the University, and as a result, it is vital they keep staff informed of any changes as a result of their review.
- Reporting line details for staff have been captured from University HR systems at a point in time. Where Managers identify incorrect reporting relationships as part of this review, they are requested to update details via MyUNSW or contact the HR Business Partnering team for assistance.
- There is no immediate action required by staff using applications under review. Any questions about access should be directed to their manager/supervisor.
- Communications will be sent from the Cyber Security UAR mailbox directly to involved Business Owners and reviewers (UNSW Managers/Supervisors) by the Cyber Security UAR Team.
- For full details refer to the Cyber Security Guideline - User Access Review.
-
User account/ access type Action Duration Escalation
(and duration)Reviewer: Business Owner Privileged accounts - Re-validation of access, or
- Deletion or de-activation of account
Note: Delegate can be an IT Service Owner. Privileged accounts certified by the delegate, must then be re-certified by the Business Owner.
15 working days Manager once removed (MoR)
(10 working days)
Elevated accounts
(IT related)- Re-validation of access, or
- Deletion or de-activation of account.
Note: Delegate can be an IT Service Owner. Elevated access certified by the delegate must then be re-certified by the Business Owner.
Elevated accounts
(Business function-related)- Re-validation of access, or
- Deletion or de-activation of account
Note: Delegate can complete the review.
Reviewer: UNSW Manager (of staff) Standard user account - Re-validation of access, or
- Deletion or de-activation of account
Note: Delegate can complete the review.
15 working days Manager once removed (MOR)
(10 working days)
Important
- Where an assigned UAR has not been completed in 15 working days by the reviewer (Business Owner or UNSW Manager/Supervisor, or their delegate), the Manager once removed (MoR), of the user or account concerned, will be required to complete the UAR in 10 working days.
- Reporting line details for staff (accounts) are sourced, at a point in time, from information in HR systems. To ensure this information is accurate, Managers/Supervisors should review their staff reporting details via MyUNSW or contact the HR Business Partnering team for assistance.
- For full details refer to the Cyber Security Guideline - User Access Review
Reporting cyber incidents
It is important to report any cyber security incidents as quickly as possible so that UNSW IT’s Cyber Security team can address any issues and mitigate risk exposure.
What should I report?
- Suspecting your computer or account has been compromised.
- Having evidence on how technology or University data may be vulnerable.
- Noticing a colleague inappropriately sharing Highly Sensitive or Sensitive data.
- Losing a University asset containing sensitive information.
Report a cyber security incident by calling the UNSW IT Service Centre on 02 9385 1333 or using the link below.
Cyber security is everyone’s responsibility and by learning a few rules, simple steps, and following guidelines, we can protect ourselves and our University from cyber security threats and keep data safe. Go to Cyber Security Training and Awareness for more information.